


Overview
.jpg)



Ever since the end of the cold war and throughout the conflicts of the 1990s and the early 2000s, Unmanned Aircraft Systems (UAS) or drones have obtained an increasingly prominent battlefield presence in roles ranging from Intelligence, Surveillance, Target Acquisition, and Reconnaissance (ISTAR / ISR) to combat missions such as multi-use UCAVs or single-use kamikaze drones and loitering munitions.
In civilian applications, drones are now commonly used in law enforcement, agriculture, oil & gas, energy, and logistics for everything from crop spraying to pipeline inspections.
In this blogpost we will present a brief overview of common UAS radio links, especially as seen in FPVs, discuss why analog video links are still around, and briefly go over historical drone video feed interception incidents in military contexts in Lebanon, Iraq, Syria, and Israel.
In part 2 we will discuss the relevance of (analog) video links to Counter-UAS measures and the (in)security of video scramblers.
In what has been called the FPV revolution, cheap, disposable, and easily assembled and modified small UAS with technological roots in the First-Person View (FPV) drone racing hobbyist environment have seen heavy military equipment destroyed in bulk on both sides of the Russia-Ukraine war while drone-saturated kill zones have driven the frontlines into a stalemate.
FPV kamikaze drones played a key role in the Ukrainian Operation Spiderweb targeting Russian Air Force bases deep inside Russia. A similar deep strike operation using small drones was undertaken by Israel against Iran during the 12-Day War of 2025. Likewise, Iran's mass produced, comparatively cheap Shahed kamikaze drones (and their export to Russia and subsequent adaption into the GERAN) have been used in waves in Ukraine for years and played an outsized role in the 2026 Iran war.

While those conflicts have been the most visible, they are not exceptions. In the past 5 years alone, the prominent usage of cheap DIY drones by under-resourced militias in the Myanmar Civil War and of heavier types of drones everywhere from the Sudanese Civil War to the Second Nagorno-Karabakh War and Operation Sindoor has led analysts to ask whether all wars are now drone wars.
Drone security concerns are not restricted to open warzones either, as evidenced by the 2019 drone strikes on Saudi oil refineries and by a series of mysterious drone sightings near European airports and military bases in 2025 which were largely claimed to be Russian hybrid warfare signaling activity. Mexican drug cartels have also increasingly adopted FPV drones for purposes ranging from attacks on rivals and security forces to ISR and smuggling.
As such UAS of all sorts are highly interesting from a cyber / Electronic Warfare (EW) perspective, both in thinking through how to detect them, extract intelligence from them, and disrupt them as well as how to harden them against such measures. EW based Counter-UAS (C-UAS) measures were cited as a major obstacle to the Indian military's use of drones in Operation Sindoor.
It is important to acknowledge that EW measures in C-UAS are a rapidly evolving field. Especially in the Russia-Ukraine war, the widespread use of COTS components, open-source firmwares, and Software Defined Radio (SDR) components has allowed for rapid measure/counter-measure development cycles leading an article in IEEE Spectrum to dub it the first Hacker's War. The space is also neither uniform nor with clear directionality, what may be obsolete in one conflict zone (Ukraine) may be considered emerging tech in another (Myanmar), lessons learned by one military unit may not be quickly shared and distributed with others, and operators may find themselves coming back to technologies found vulnerable to one threat (eg interception) in the face of another (eg jamming) if the trade-off makes sense.
UAS have lot of interesting aspect fom a cyber / Electronic Warfare (EW) perspective but of primary interest are their radio links. Not all UAS have such links, some use a combination of AI, computer vision, and on-board map data to navigate, or make limited use of GNSS augmented with Inertial Navigation Systems (INS), and others are controlled through tethered (fiber-optic) links. Still, many UAS (especially those with ISR or roaming combat missions) will have one or more of the below radio links.
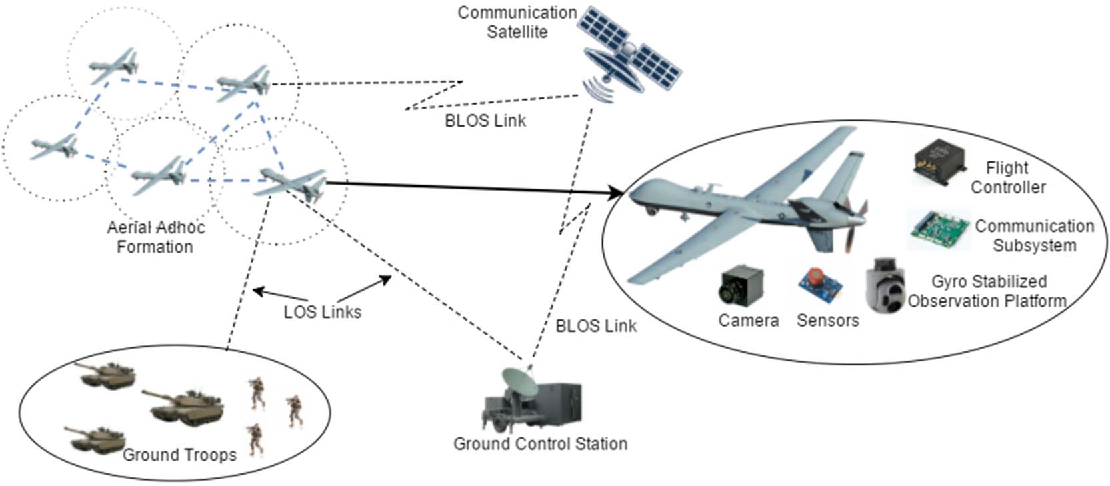
The typical UAS setup will include a Ground Control Stations (GCS) or individual operator somewhere in the (relative) vicinity of the UAS area of operations. Operators here will communicate through Line of Sight (LOS) links. Operational range can be extended with Beyond Line of Sight (BLOS) capabilities in the form of either an on-board cellular modem (4G/5G) connecting to a local Mobile Network Operator (MNO), an on-board SATCOM terminal, or a (mesh) network of relay drones all relaying communications between a more remote GCS and the UAS. These types links can also co-exist, with a LOS video feed downlink being active next to a BLOS remote control link if the goal is for the UAS to make video available to local operators.
Navigation links in their simplest incarnation are just a GNSS module. For UAS operating in more EW-contested areas, these will include various modifications such as supporting and cross-checking multiple GNSS constellations (e.g. GPS, Galileo, BeiDou), including anti-EW sanity checks, using CRPA antennas, integrating non-GNSS Position, Navigation, and Timing (PNT) signals, and navigating using Signals of Opportunity (SoOp).
For commercial drones or military drones with a consumer FPV technology legacy, these links typically operate in the 868/900 MHz and 2.4 GHz bands. Popular protocols used for manual control RC in FPV drones include ExpressLRS (ELRS), TBS Crossfire (CRSF), ImmersionRC Ghost, and FrSky SBUS.
One top of such radio links, more complex telecontrol and -telemetry protocols such as MAVLink, LTM Telemetry, and MultiWii MSP can be carried for transmitting basic telemetry (UAS position, altitude, battery and subsystem health status, etc.) and control commands (loading new maps, setting waypoints, etc.). Military drones that come out of the established defense primes (such as the ScanEagle, BlackJack, or Raven) use proprietary link types that have little in common with what can be seen in the FPV space.
Video feed links are present in almost all drones (with some exceptions like long-range kamikaze drones) since the 1980s, being integral to piloting operations and mission payloads such as mapping/survey footage, tactical ISR, or post-strike battle damage assessments.
There's a massive ecosystem for link types out there, especially in the FPV-derivative space, without too much of a global monoculture having emerged yet. For FPV drones there are typically two types of video links (handled by a Video Transmitter / VTX and Receiver / VRX):
Payload data links are distinct from the more conventional video feed, especially where packages are concerned that include specialized cameras, radars, LiDAR, or SIGINT transceivers. These links tend to be high-bandwidth and as such trade-offs have to be made with other radio links, typically resulting in bulk payload data being stored on-board with only high-priority data or summaries being streamed in real time.
Drone-to-drone communication links can be used for swarm coordination (position, intent, and task coordination) as well as mesh network for payload, control, and video relaying for BLOS purposes.
While using analog video links may feel outdated, and many high-end military UAS tend to relay digital video feeds over Ku-band SATCOM BLOS links, there are good reasons for analog's historical dominance other than technical inertia.
First of all, many electro-optical (EO) sensors have analog outputs in NTSC/PAL formats which have to be digitized either on-board (historically quite heavy) or result in a combined analog/digital downlink. Secondly, video quality degrades more gracefully than digital. In digital signals, interference (atmospheric, inter-component, EW) will often result in corrupt bitstreams and checksums requiring more complicated error correction and fault tolerance schemes. In analog video, mild or limited interference will only result in partial image corruption with some grace period before signal loss that allows UAS operators to take corrective piloting or mission payload actions (provided telecontrol links remain unaffected). Finally, analog video links are cheaper and simpler to integrate into heterogenous ecosystems where others who may require video feed access do not have the right components for a digital link.
The major downside, of course, is that analog signals cannot be securely encrypted in the same way that digital signals can be due to the nature of dealing with continuous vs discrete signals - instead relying on less secure scrambling techniques. The absence of a digital signal also significantly complicates key management, since secure analog OTA key exchange is impossible.
While most people (rightfully) don't see the risks of using analog video feeds in hobbyist FPV drones, below we will discuss just how prevalent analog video feeds were in military UAS and in some cases - still are. NATO even has the dedicated STANAG 3350 standard for analog video and a wide array of domestic UAS operated by the DOD, DOI, DOJ, and NASA were listed at least in 2015 to still transmit analog video feeds over the L-band.

The RQ-2 Pioneer was a joint US-Israeli developed UAV introduced in 1986 and widely deployed during the 1991 Gulf War, the Somali Civil War, the NATO interventions in former Yugoslavia, and the Iraq war. Operators historically included the US Navy, Army, and Marine Corps, the Sri Lanka Air Force and Navy, and the Republic of Singapore Air Force and it is still in-use as a training UAV with some forces. The Pioneer has the dubious honour of being the first documented instance of humans surrendering to an unmanned vehicle when 40 Iraqi soldiers on Faylaka Island surrendered to an RQ-2, foreshadowing the haunting footage of soldiers in the Russia-Ukraine war (attempting to) surrender to drones. The RQ-2 was outfitted with gimbaled electro-optical/infrared (EO/IR) sensors which provided analog video streaming via C-band Line-of-Sight (LOS) links.

The MQ-1 Predator is, together with the MQ-9 Reaper, arguably one of the most famous military drones from the War on Terror era and was heavily utilized in the United States' targeted killing program. While officially retired by the US and UK, a number of Predator drones were delivered to the Royal Moroccan Air Force in 2013 and the UAE Air Force in 2017. The Italian Air Force retired their Predator drones in 2022. The MQ-1 used a C-band LOS data link transmitting NTSC analog video.

The MQ-27 ScanEagle, which entered service in 2005, is one of the most popular ISR UAVs and has seen numerous deployments in just about every military and counter-insurgent conflict of the 21st century as well as various counter-narcotics and counter-piracy operations. It is operated by all Five Eyes countries, as well as several European, South-East Asian, and Latin American countries. Historically, it operated an S-band 2.4 GHz analog video feed in NTSC format from an Alticam 400 camera turret.
Around 2009, ViaSat / EnerDyne started supplying its EnerLinks DVA (Digital Video over Analog) technology for integration with the ScanEagle in order to allow for carrying AES encrypted digital links over older analog FM links without requiring RF equipment overhauls. Further digital datalink upgrades have become available over the years, such as the L-3 Bandit O-QPSK modulated datalink which operates in the L-/S-/C-bands. Integration of these upgrades is of course contingent upon availability to operators. The Royal Netherands Army still operated at least 6 ScanEagles with analog links in the 2012-2014 period when it fielded ScanEagles around Somalia and Mali. Somewhere before 2020 it replaced its ScanEagles with the RQ-21 Blackjack / Integrator.
Interestingly, the Iranian Qods Yasir (Sayed-2) UAV was reportedly developed through reverse-engineering a captured American ScanEagle. Apart from operation by the Iranian Army and IRGC, Yasir UAVs were also delivered to the Assad-era Syrian Army as well as (reportedly) Hezbollah and Iraqi Shia paramilitaries. While one can only speculate without access to hard technical facts it seems unlikely any of the datalink upgrades available to the ScanEagle would have been similarly incorporated in the Yasir.
.jpg)

The hand-launched RQ-11 Raven, which went into full production in 2006, is one of the more popular military Small UAVs (SUAVs) and is operated by armed forces from Five Eyes, European, and Middle Eastern Countries. Originally, all Raven variants (RQ-11A) used an 4-channel analog data link with downlink in the L-band which was superceded in the 2008-2012 period by AeroVironment's Digital Data Link (DDL). DDL is listed as operating in the L- and S-bands, specifically the military microwave M1-6 frequency bands: 1625-2510 MHz (with various public documents indicating M1 and M2 usage).
An analog variant (sometimes referred to as Raven B or RQ-11B) remained in service with many operators however, with US marines using it in both Iraq and Afghanistan in 2012 and the Royal Netherlands Army upgrading their analog Raven B NLD fleet to DDL only in 2016 (in addition to procuring additional RQ-11B DDL variants). Controversially, RQ-11B UAVs provided by the US to Ukraine as part of a 2015 aid package (and said to be identical to those procured by Spain the same year) were found to use analog data links rather than DDL and as such susceptible to jamming and interception by the pro-Russian separatist forces they were targeting. Reportedly, this was the result of export restrictions which has interesting implications for other recipients of such UAVs.
In 1997, during the South Lebanon Conflict, Hezbollah managed to ambush and kill 12 Israeli soldiers around Ansariya. In August 2010 Hezbollah revealed they managed to pull of this ambush because they had been intercepting analog video feeds from Israeli drones since at least 1996. Subsequent investigations suggested Hezbollah had developed this technical capability independently, rather than relying on Syrian or Iranian SIGINT capabilities or being provided video access via HUMINT sources.

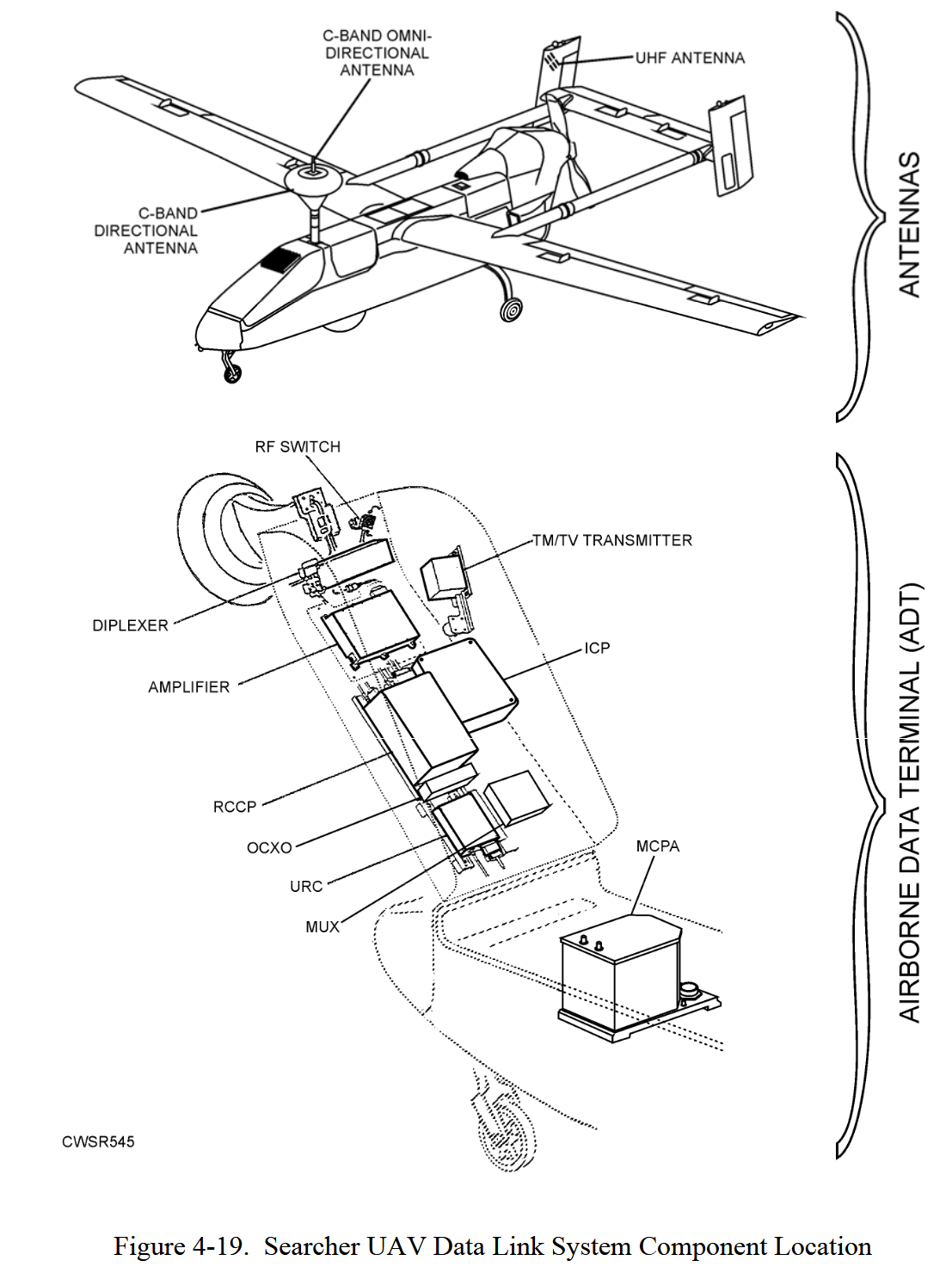
In the Ansariya Ambush, the likely culprit was probably an IAI Searcher with later claims by Hezbollah that they had intercepted IAI Searcher video footage on multiple occasions lending extra credence. Older manuals for IAI Heron and Searcher UAS also clearly confirm these UAS used analog video downlinks in the C-band where LOS communications where concerned.
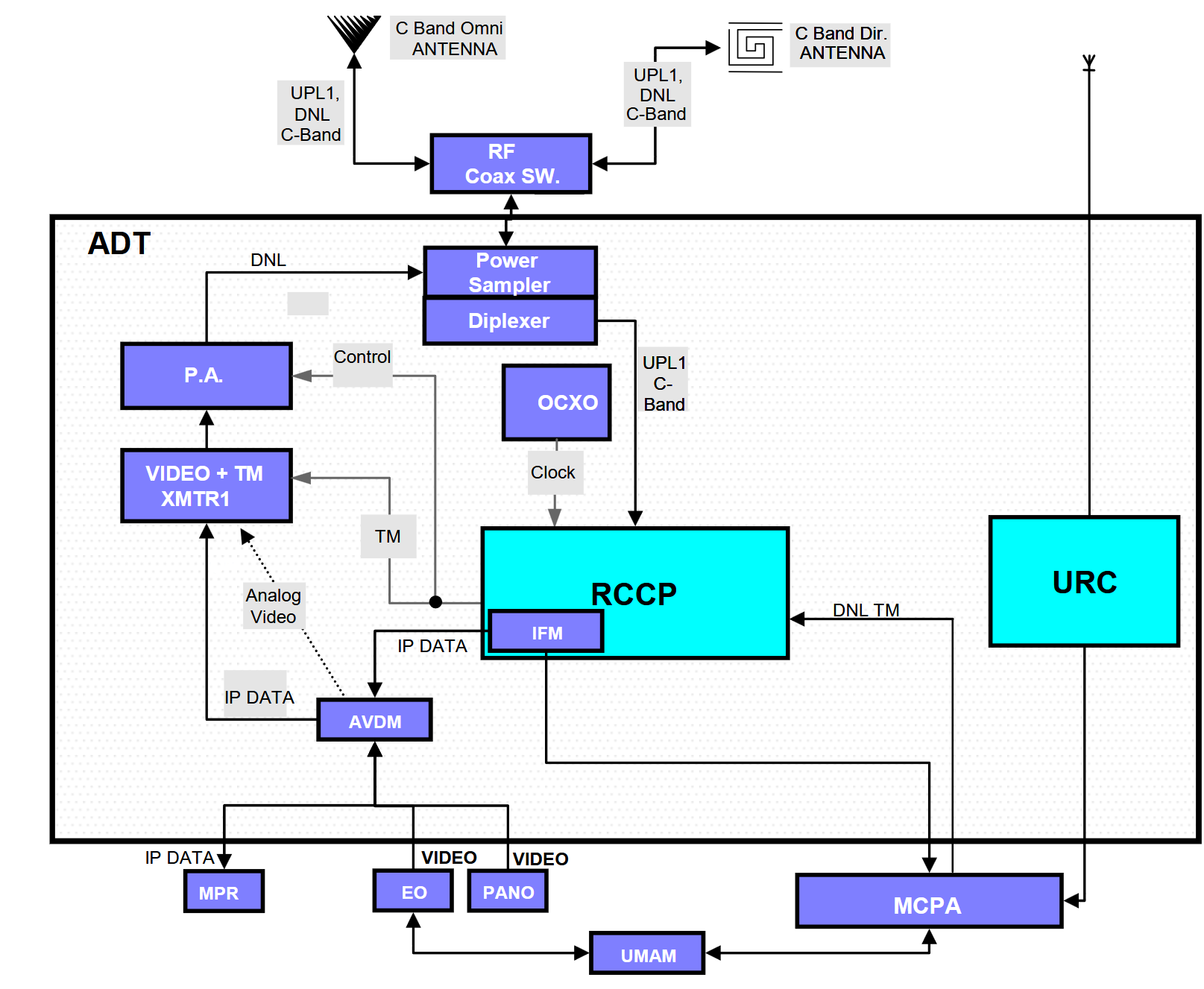
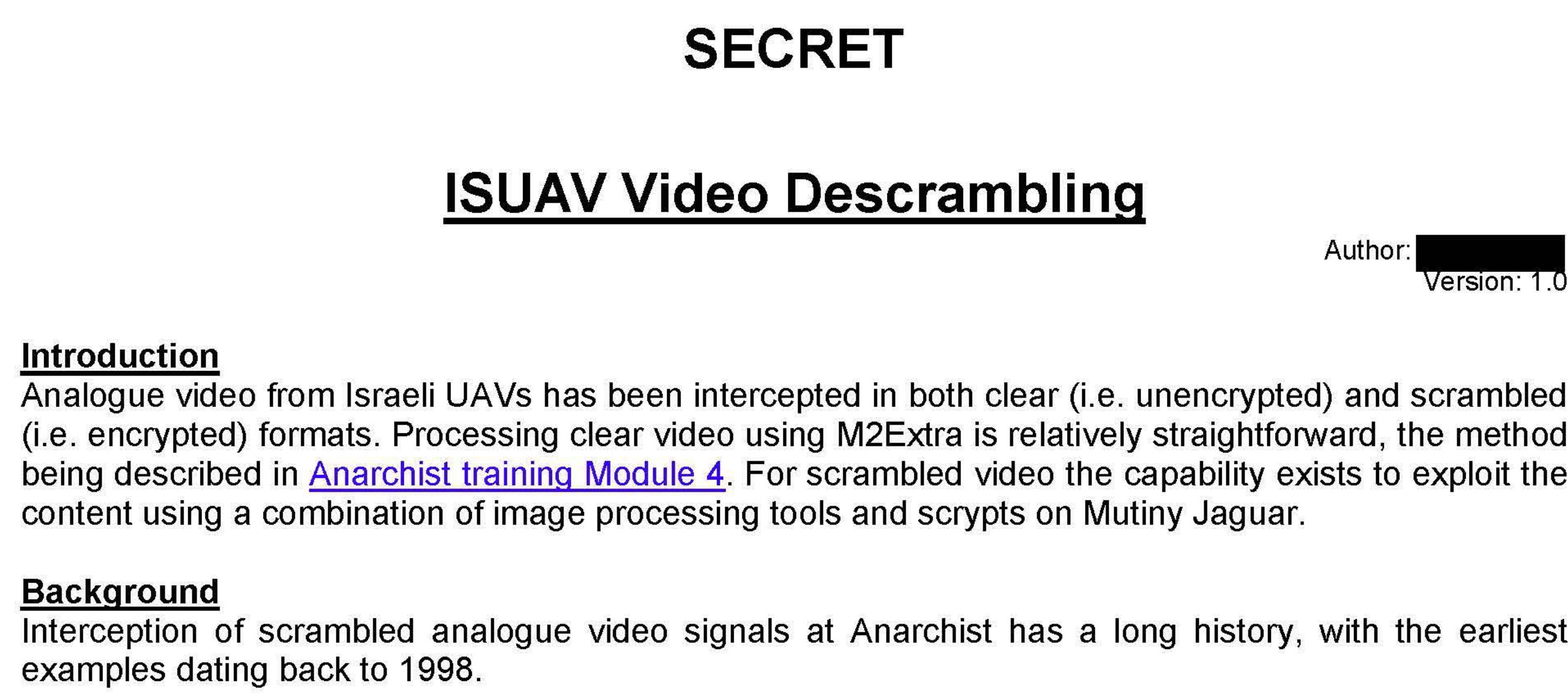
As a response to the ambush, Israeli UAVs started being outfitted with video scramblers with GCHQ documents leaked as part of the Snowden files describing picking up scrambled Israeli UAV video signals as early as 1998.
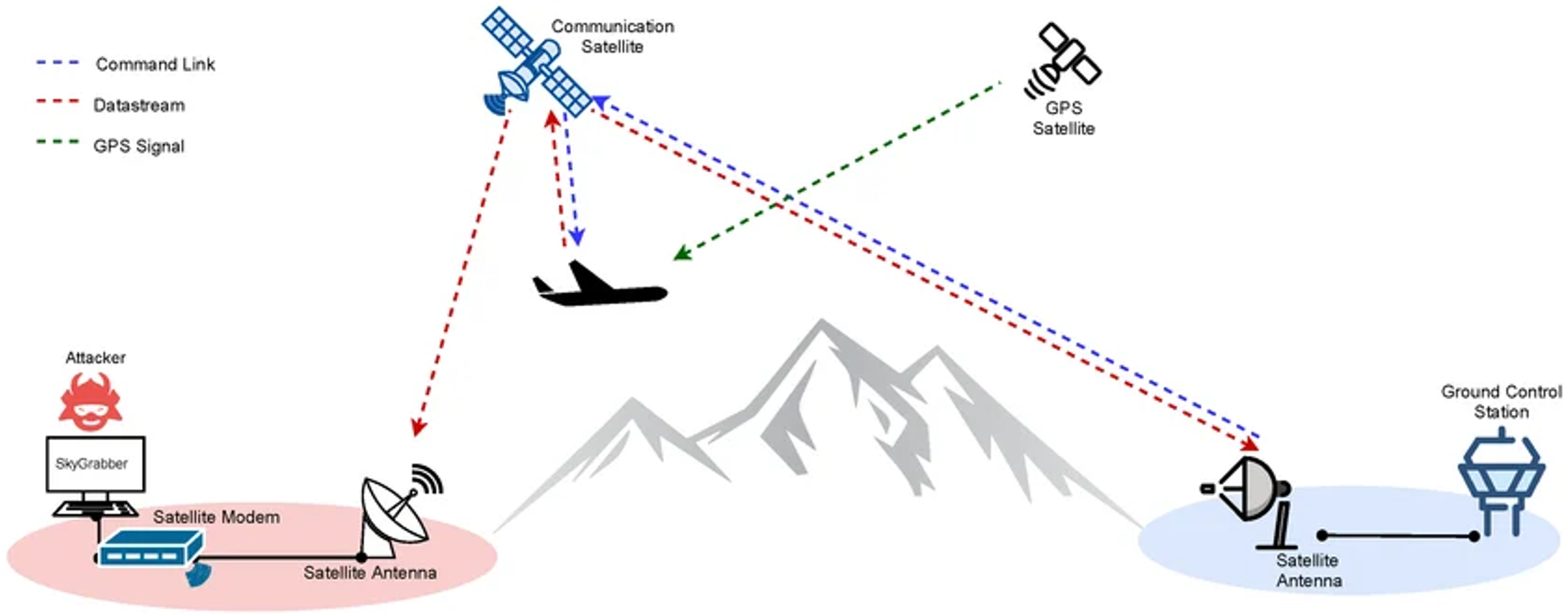
A widely reported incident in 2009 saw Iraqi insurgents intercept video footage from US MQ-1 Predator drones using the commercial SkyGrabber software. While Predator drones originally used a C-band LOS data link transmitting NTSC analog video, and US Air Force documents stated as far back as 1999 that Predator data links were unencrypted, this was reportedly not the culprit in this incident. Instead, Predators could eventually transmit video feeds over BLOS Ku-band SATCOM uplinks and US troops (in particular Joint Terminal Attack Controllers (JTACs) and special forces) would receive video feeds on satellite downlink to so-called Remotely Operated Video Enhanced Receiver (ROVER) terminals rolled out in 2002.
However, ROVER rollout was apparently done so hastily that terminals could only receive unencrypted L/C/S/Ku-band SATCOM downlinks. As such, Predators may have uplinked video feeds in encrypted form but the satellites then broadcast the footage in plaintext on the downlink - allowing anyone with the SkyGrabber software to intercept them. Other ROVER-linked UAS (such as the RQ-7B Shadow) were likely similarly affected.
This incident is remniscent of a 2005 CIA report which mentions that in the lead-up to the Iraq war a young, technically capable relative of Saddam Hussein was assigned to the Baghdad Aerospace Research Center where he reportedly intercepted real-time overhead UAV videos of U.S. military installations in Turkey, Kuwait, and Qatar from unencrypted satellite downlinks.
In 2016, reporting based on leaked GCHQ and NSA documents from the Snowden files [1,2] revealed the existence of a joint NSA-GCHQ program called Operation Anarchist which collected (among other things) UAV video footage from the Middle East through Troodos and Menwith Hill stations.
These documents show video intercepts from the Israeli Heron TP, IAI Searcher MK3, and Aerostar Tactical [1,2] UAS (all of which had been in wider global use beyond Israel) which are documented to have used (at least in older versions) LOS datalinks carrying analog NTSC/PAL video over the L/S/C-bands. In 2025, Germany was purchasing new Heron TPs, the Indian Air Force continued to operate IAI Searcher Mk2 (and Russia continued to operate its Forpost copy), and Azerbijan paraded around its Aerostar Tacticals which it produces domestically. And while it seems unlikely (though not impossible) analog video downlinks are still prevalent on those newer versions it does show older UAS phased out in one part of the world can have a long afterlife elsewhere.
The documents mention that while digital link upgrades to normal analog video signals were observed, regular intercepts of scrambled analog video feeds were still made at the time (which we have analyzed in-depth in a previous blogpost). Given Hezbollah's ability to intercept Heron and Searcher footage, it is unsurprising GCHQ/NSA were doing the same.
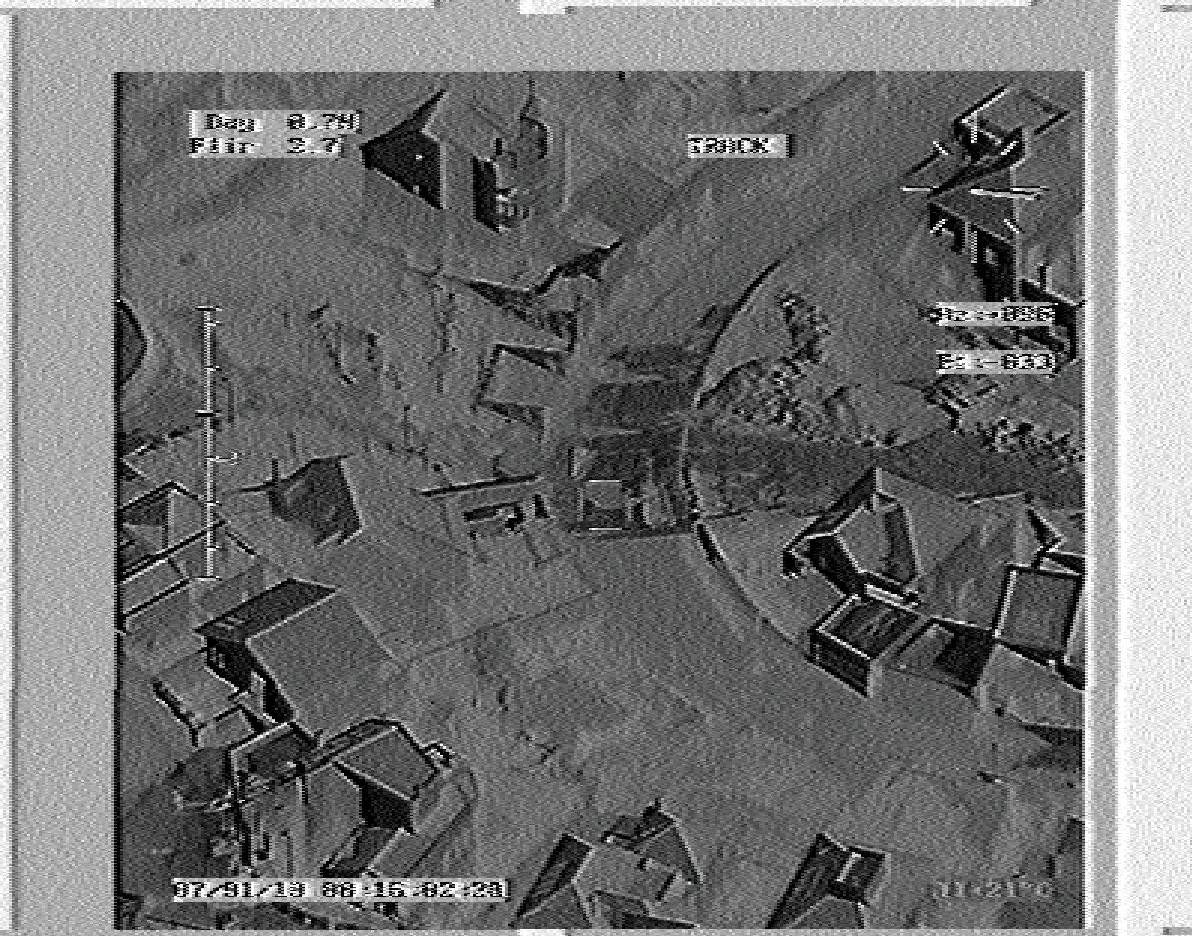
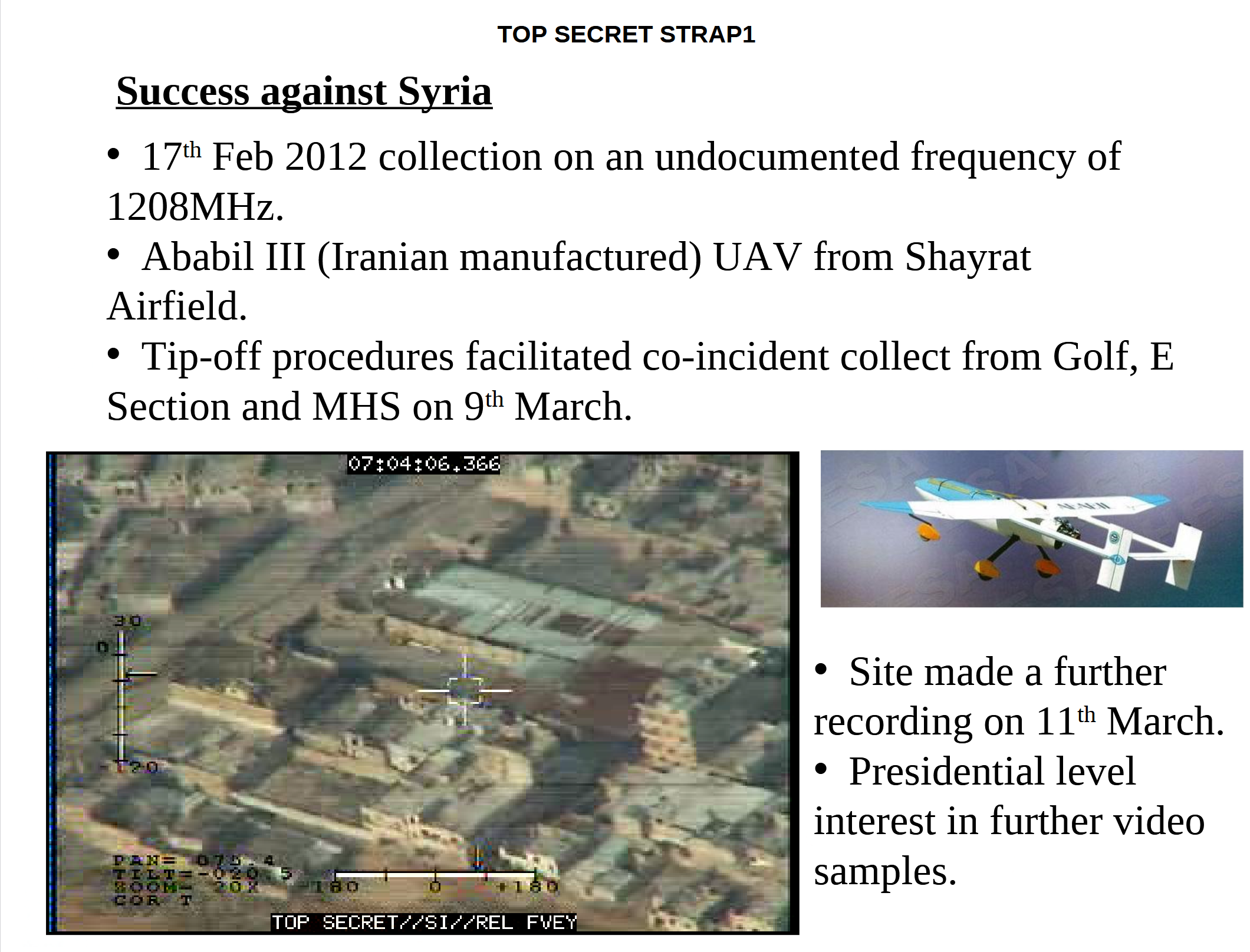
The documents also mentioned intercepts from an Iranian HESA Ababil-3 UAS operated by Syria which received presidential level interest. The Ababil-3 is primarily an ISR drone and outside its active use by Iran has been widely exported (including to Sudan and Iraqi Shia militias) and extensively used during the Syrian Civil War. Its predecessor, the Ababil-2, has been exported to both Hezbollah and the Libyan National Army. The Ababil-3 is reportedly based on the South African Denel Dynamics Seeker and operates an analog video downlink on 1208 MHz.
In part 2 of this series we will discuss the relevance of analog video links to Counter-UAS measures and the (in)security of analog video scrambler approaches.
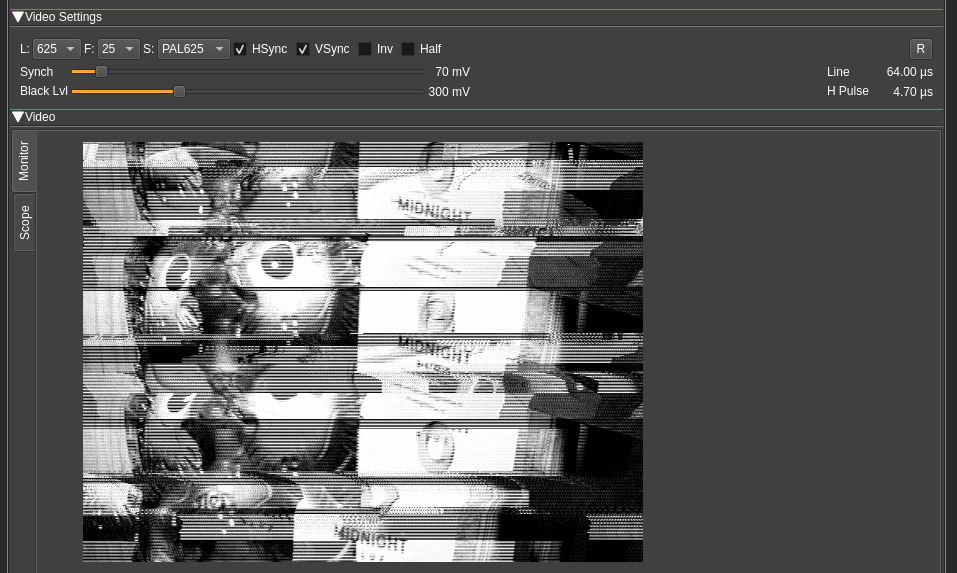
For those interested in advancing their RF security skills, including analyzing drone RF links, Midnight Blue will be delivering its Red Team SIGINT training at several conferences:
This practically-oriented course, aimed at red team operators and pentesters, will teach attendees the fundamentals of RF, SDR, and SIGINT before quickly moving on to effective guidance on identifying and decoding unknown signals as well as exploiting common pitfalls in RF security.
Where other SDR trainings tend to focus on enterprise and IoT RF protocols such as 4G/5G, WiFi, RFID, and BT, this training focuses on important but rarely addressed RF technologies such as automotive, aviation, marine, and physical access control RF protocols and mission-critical radio (e.g. TETRA, DMR, P25) used by police, military, private security, and critical infrastructure.
Hands-on exercises such as intercepting and decrypting handheld radio comms, analyzing drone video feeds and maritime RF communications, and breaking automotive security systems are alternated with thorough overviews of relevant RF protocols and their security posture as well as case studies of real-world RF attacks on railways, water utilities, drones, and police/military radios.
An overview of the course can be found here.


All items